This tutorial will describe how you can join machines that run Linux Mint 17.1 OS to Windows 2012 Active Directory Domain Controller in order to authenticate remote accounts from AD back end identity provider to local Linux workstations with the help of SSSD service and Realmd system DBus service.
The System Security Services Daemon (SSSD) is a relative new service which provides cross-domain compatible methods for Active Directory users to authenticate to local machines using a combination of usernames and domain back end name to create the login identity, even if the Domain Controller goes offline (SSSD caches credentials).
REQUIREMENTS
- Windows Server 2012 configured as an Active Directory Domain Controller
- A Linux Mint 17.1 client machine which will be integrated to Windows PDC
Domain Settings:
- Domain Name:
caezsar.lan - Windows Server 2012 AD FQDN:
server.caezsar.lan - Windows Server 2012 AD IP Address:
192.168.1.130 - Linux Mint Hostname:
mint-desktop - Linux Mint IP Address: automatically assigned by DHCP
- Linux Mint first DNS IP Address: Manually assigned to point to AD PDC –
192.168.1.130
STEP ONE – Linux Mint Network Configuration
1. Before starting with installing the required services in order to integrate the local machine to the PDC Server, first we need to assure that Windows Domain Controller is reachable through DNS resolution on Linux Mint host by adding the DNS PDC IP Address on our Network Configuration. To achieve this goal, first open Network Settings, go to the Network Interface Card (in this case is the Wired Connection, but you can use a Wireless Connection also), open it for editing (hit the settings icon from bottom right) and add your PDC IP Address on IPv4 DNS filed (switch Automatic DNS to OFF) as illustrated in the following screenshots:

network settings
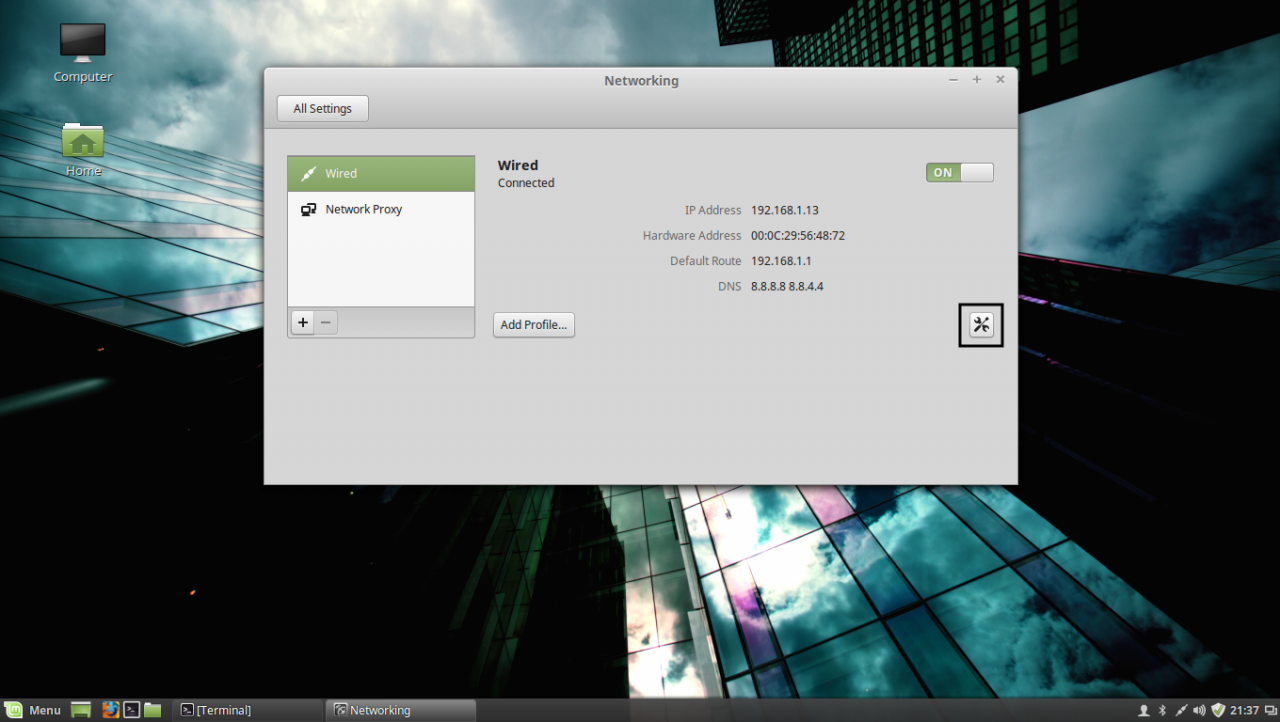
edit network interface settings
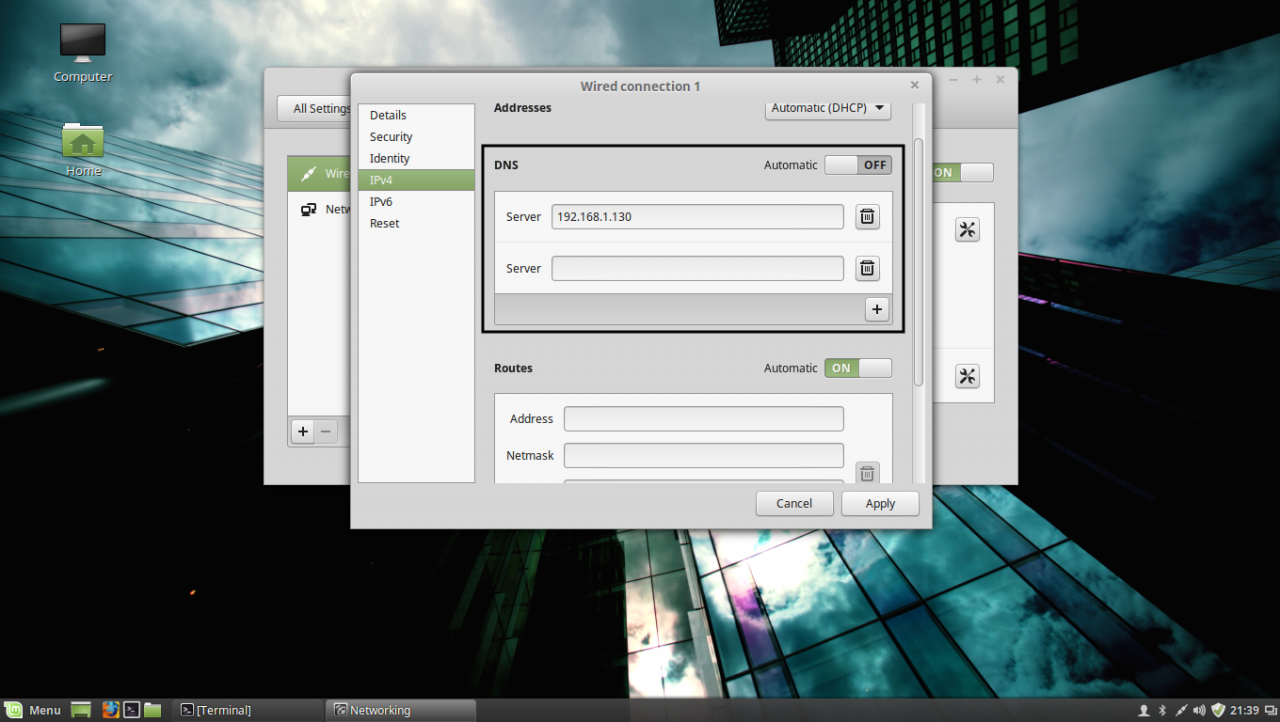
add DNS IP Address
If multiple Domain Controllers machines exists on your network then you can also add their IP Addresses on IPv4 DNS settings fields.
2. After you’re done, hit on Apply button and switch the edited Network Interface from ON to OFF and then back to ON in order to apply the new settings. After the network interface is started again, open a Terminal console and issue a ping command against your PDC domain name in order to verify if the settings are successfully applied and the domain name responds with the correct IP Address and FQDN of the PDC.
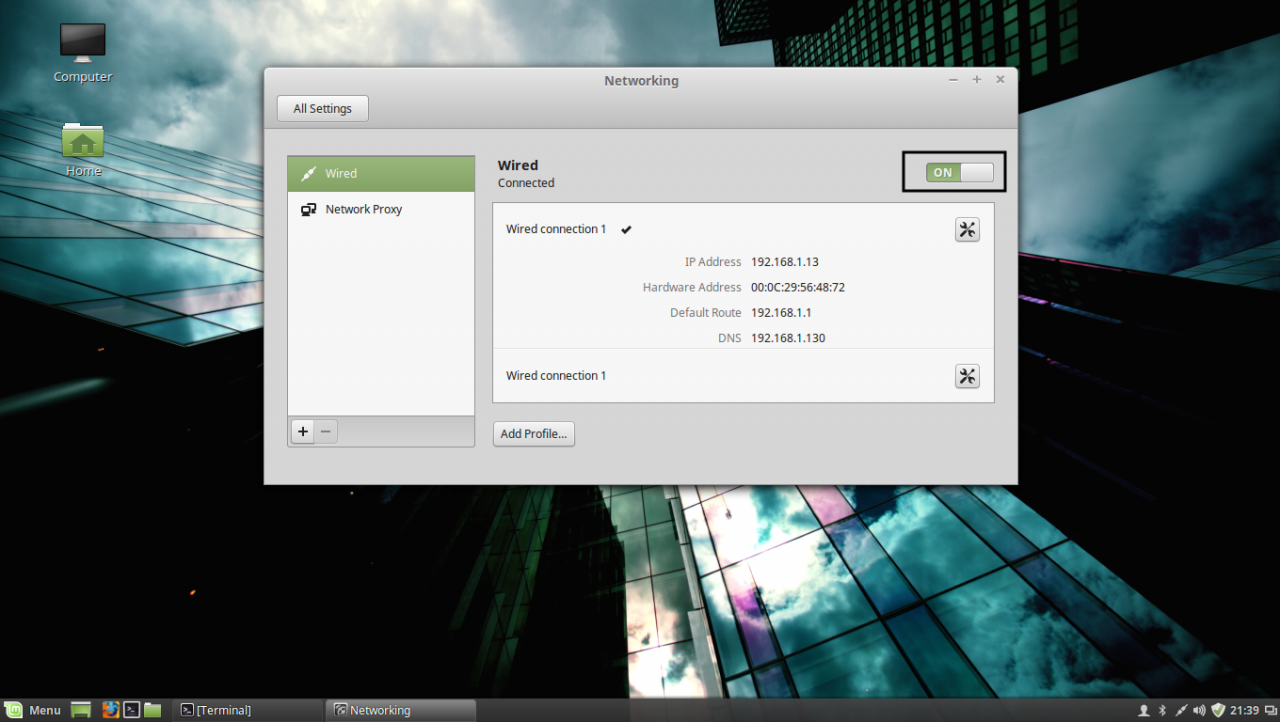
apply network settings
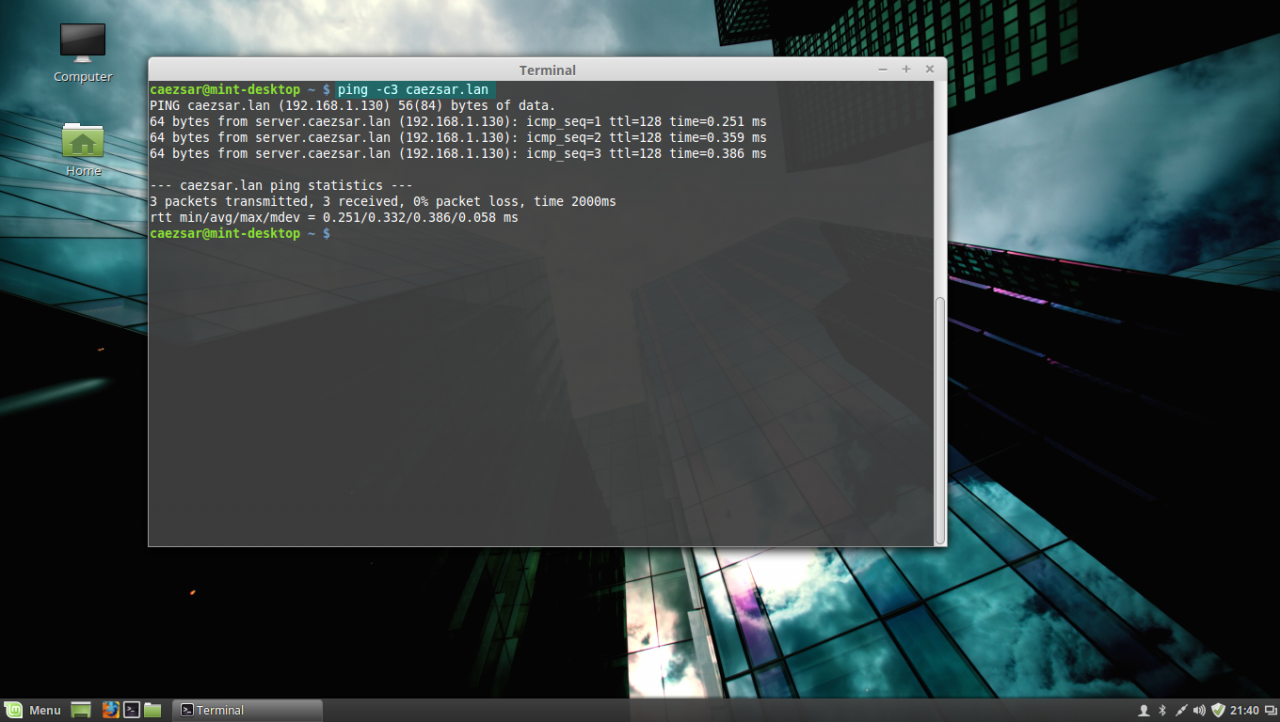
ping domain controller
If you want to avoid all this manual settings, then configure a DHCP server at your premises to automatically assign network settings, especially DNS entries, that will point to your Windows PDC IP Addresses needed for DNS resolution in order to reach the AD PDC.
STEP TWO – Install Required Software Packages
As presented at the beginning of this tutorial, in order to integrate a Linux Mint machine to an Active Directory Domain Controller you need to install the SSSD service along with the following software packages and dependency:
– SSSD service (responsible with back end realm authentication) with the following dependencies: sssd-tools (optional, but useful for sssd cache, user and groups manipulation), libpam-sss (PAM modules for local authentication) and libnss-sss (NSS modules for local DNS resolution)
– Realmd (system DBus service which manages domain integration and local resources permissions)
– The following Samba Modules: samba-common-bin and samba-libs (File sharing compatibility between Windows and Linux machines)
– Krb5-user (Client network authentication and communication with the PDC server)
– ADcli (Tools for joining domain and perform other actions on an AD)
– PackageKit (Linux cross-platform packages management for interoperabillity and user privileges for software installations)
3. Now, let’s start installing the above enumerated packages by opening a Terminal console on Linux Mint and issuing the following commands with sudo privileges:
First install Realmd and SSSD service:
sudo apt-get install realmd sssd sssd-tools libpam-sss libnss-sss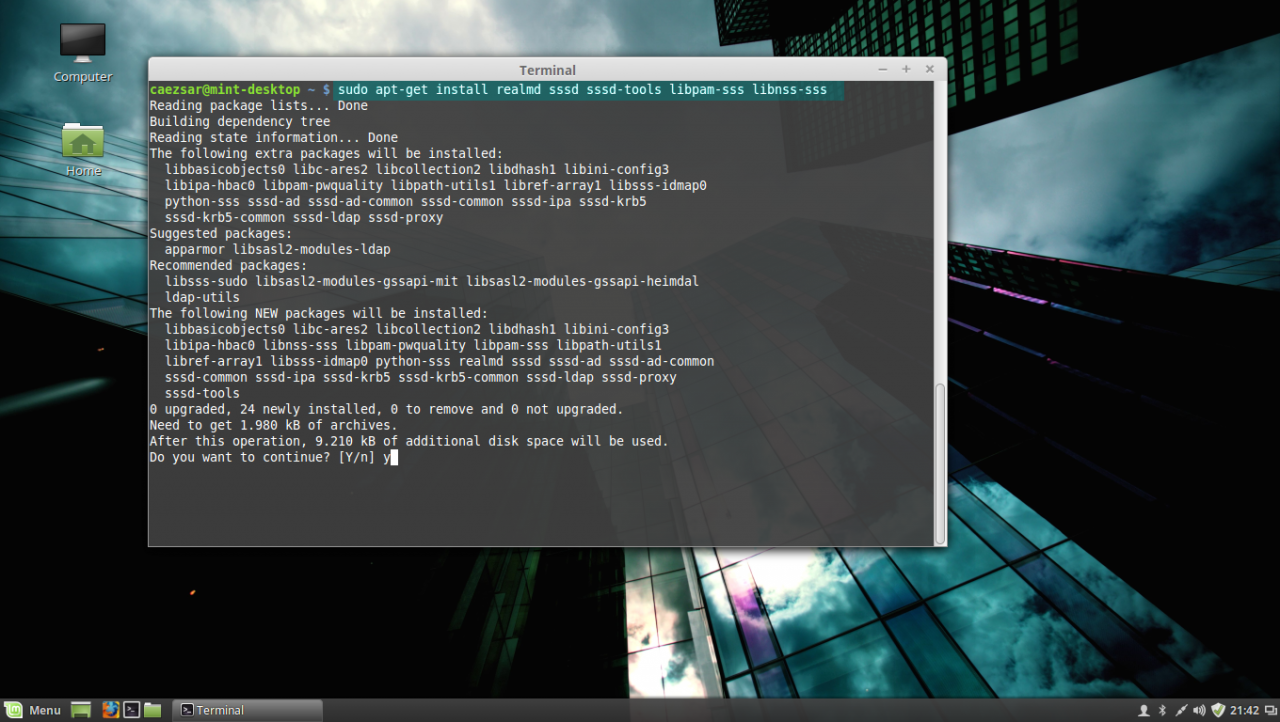
install realmd and sssd service
4. Next install Samba modules (by default this modules might be already installed on your system):
sudo apt-get install samba-libs samba-common-bin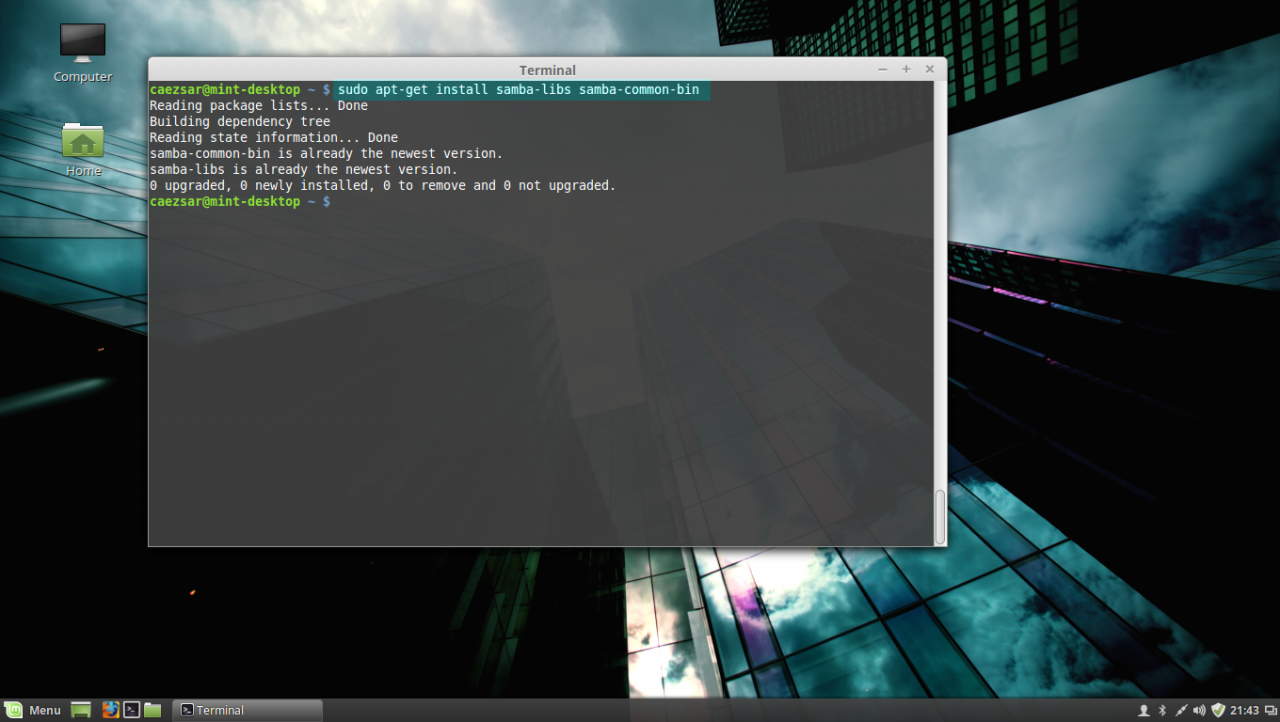
install samba modules
5. Last, install the other remained packages: krb5-user, adcli and packagekit. On krb5-user package, the installer will prompt you to enter the realm that will be used for Kerberos authentication. Use the name of the domain configured for your PDC with UPPERCASE (in this case the domain is CAEZSAR.LAN), then hit Enter key to continue further with the installation packages.
sudo apt-get install krb5-user adcli packagekit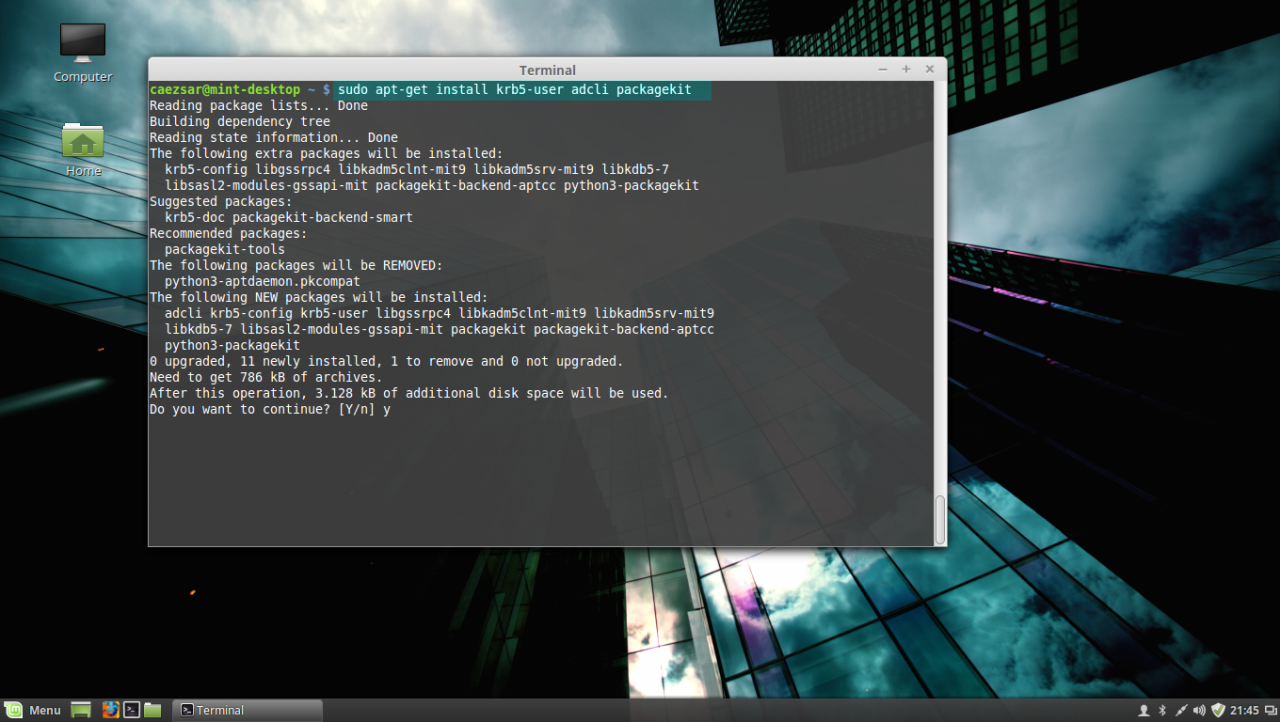
install kerberos, adcli and packagekit packages
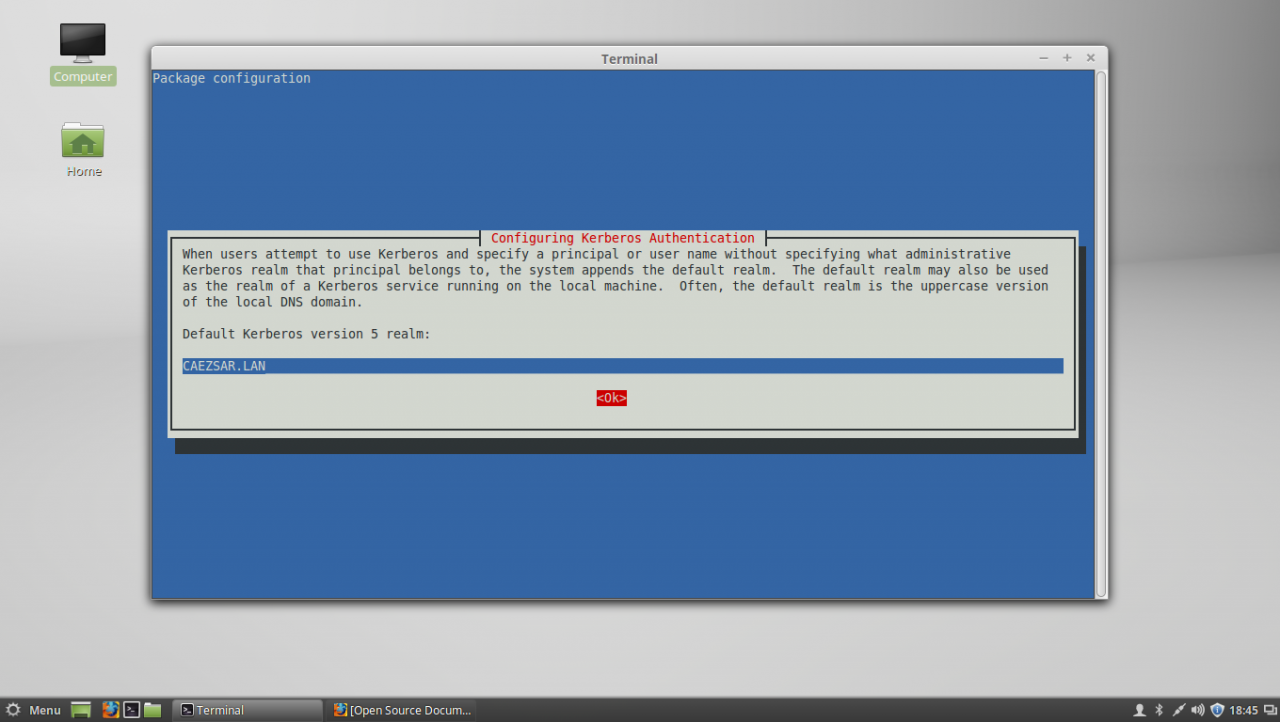
Configure Kerberos realm
STEP THREE – Edit Configuration Files for SSSD, Realmd and PAM
6. Next step before starting joining Linux Mint to Windows Server AD PDC is to configure the local services for AD network authentication. By default the SSSD service has no configuration file defined on /etc/sssd/ path. In order to create a default configuration file for SSSD service, issue the following command to create and simultaneous edit the file:
sudo nano /etc/sssd/sssd.confSSSD configuration file excerpt:
[nss]
filter_groups = root
filter_users = root
reconnection_retries = 3
[pam]
reconnection_retries = 3
[sssd]
domains = CAEZSAR.LAN
config_file_version = 2
services = nss, pam
[domain/CAEZSAR.LAN]
ad_domain = CAEZSAR.LAN
krb5_realm = CAEZSAR.LAN
realmd_tags = manages-system joined-with-adcli
cache_credentials = True
id_provider = ad
krb5_store_password_if_offline = True
default_shell = /bin/bash
ldap_id_mapping = True
use_fully_qualified_names = False
fallback_homedir = /home/%d/%u
access_provider = ad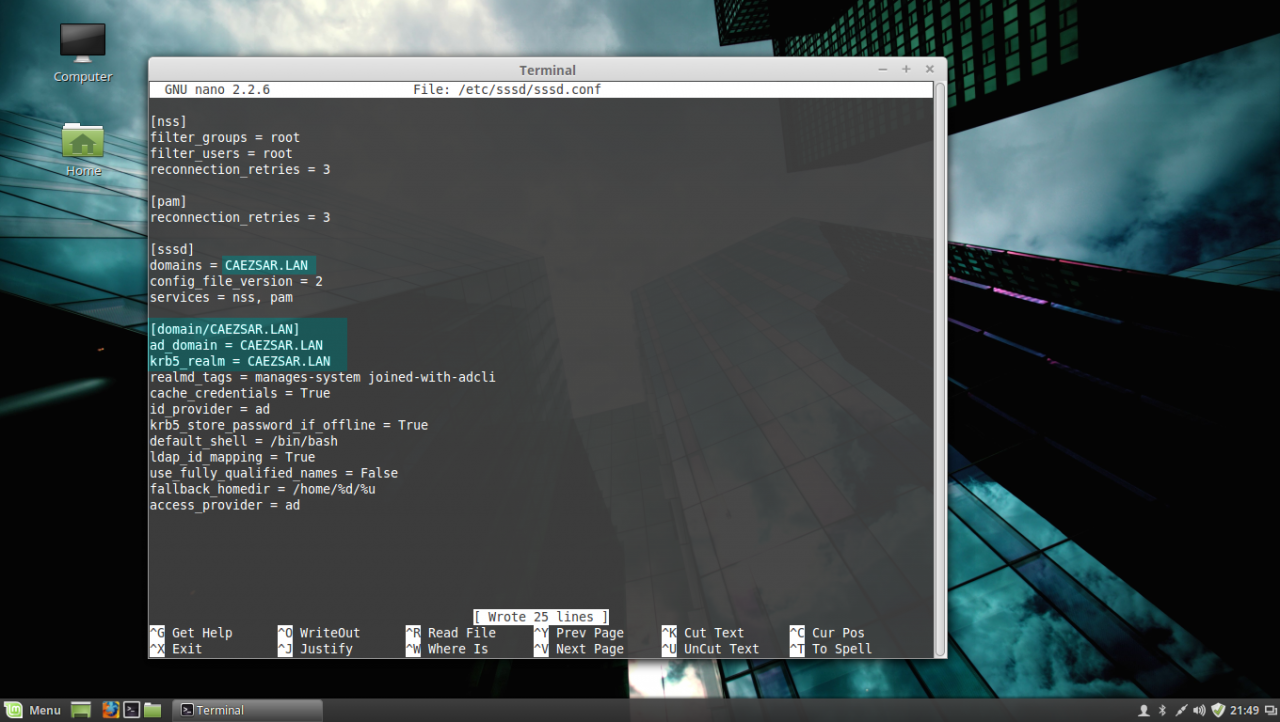
sssd configuration file
While editing the file make sure you replace domains, [domain/], ad_domain and krb5_realm parameters accordingly. Use the UPPERCASES as the above file excerpt suggests.
The fallback_homedir = /home/%d/%u parameter will cause the system to create home directories for all domain logged in users with the following path: /home/domain_name/domain_user, so practically all your domain users homes will be stored into a single directory named after your domain name on /home path. If you want to change this behavior so all domain users homes should be created as normal system users, /home/username, just remove %d variable and you’re done.
For other options and parameters concerning sssd.conf file run man sssd command.
After you finish editing the file, save it with CTRL+O , close it with CTRL+X and proceed further with the below instructions.
7. The next step is to create and edit a configuration file for Realmd in order to avoid some eventual package dependency problems by issuing the following command:
sudo nano /etc/realmd.confUse the following configurations for realmd file:
[service]
automatic-install = no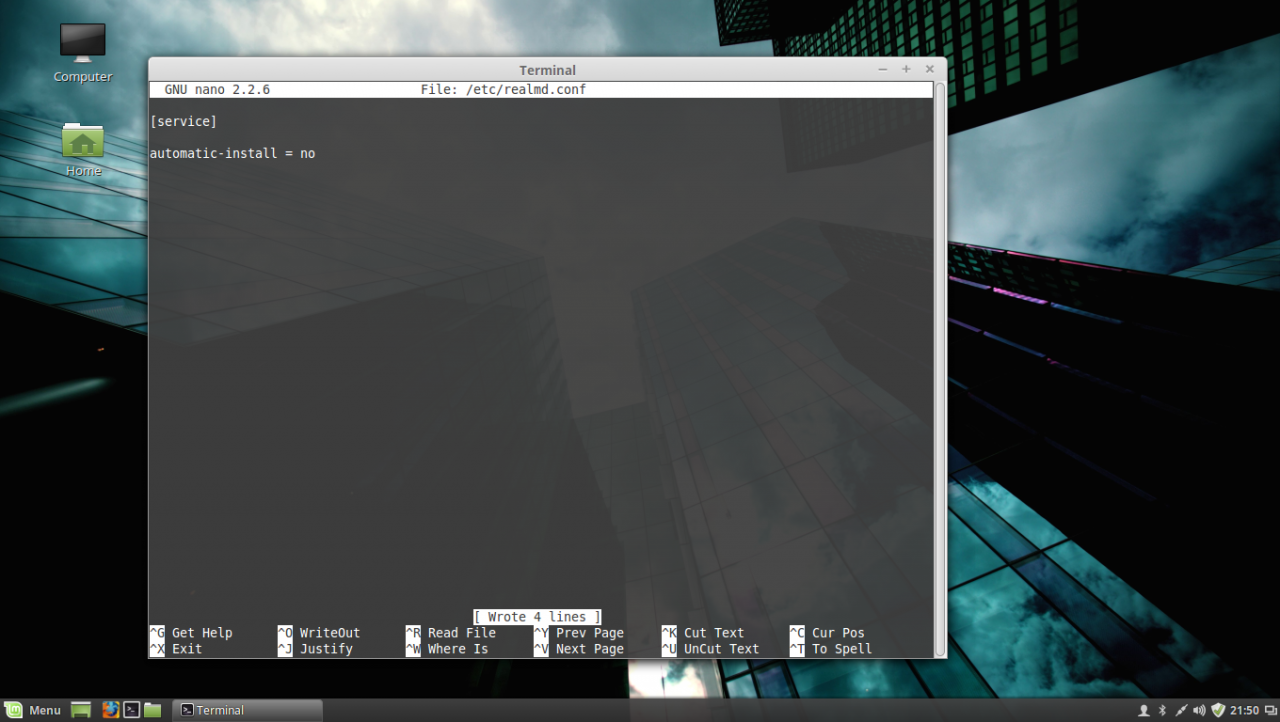
realmd conf file
After you add the above lines, save the file and close it.
8. The last file that you need to edit before joining the domain is the common-session PAM file. So, open this file for editing by running the below command and add the following line after the session optional pam_sss.so line in order for the system to automatically create home directories for the new authenticated AD users .
sudo nano /etc/pam.d/common-sessionAdd the following line as presented on the below screenshot:
session optional pam_mkhomedir.so skel = /etc/skel/ mask=0077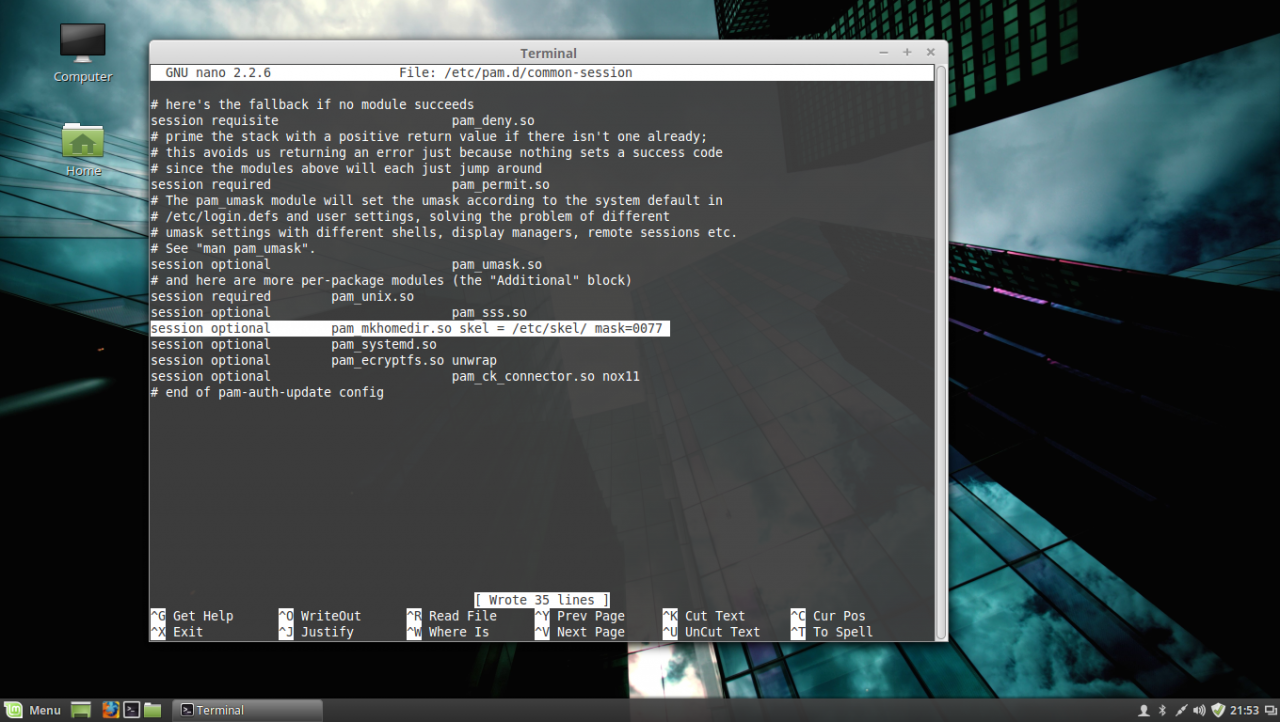
PAM common-session file
After you have edited the file, save it and close it, and proceed to the next step in order to make Linux Mint a part of the Windows Domain Controller.
STEP FOUR – Join Linux Mint to Windows Server 2012 Active Directory Domain Controller
9. Before joining the Linux Mint client to Windows PDC, first issue the discovery command against your domain name in order to view the complete realm configurations and a package list of software that must be installed on the client machine before you enroll it in the realm.
sudo realm discover domain.tld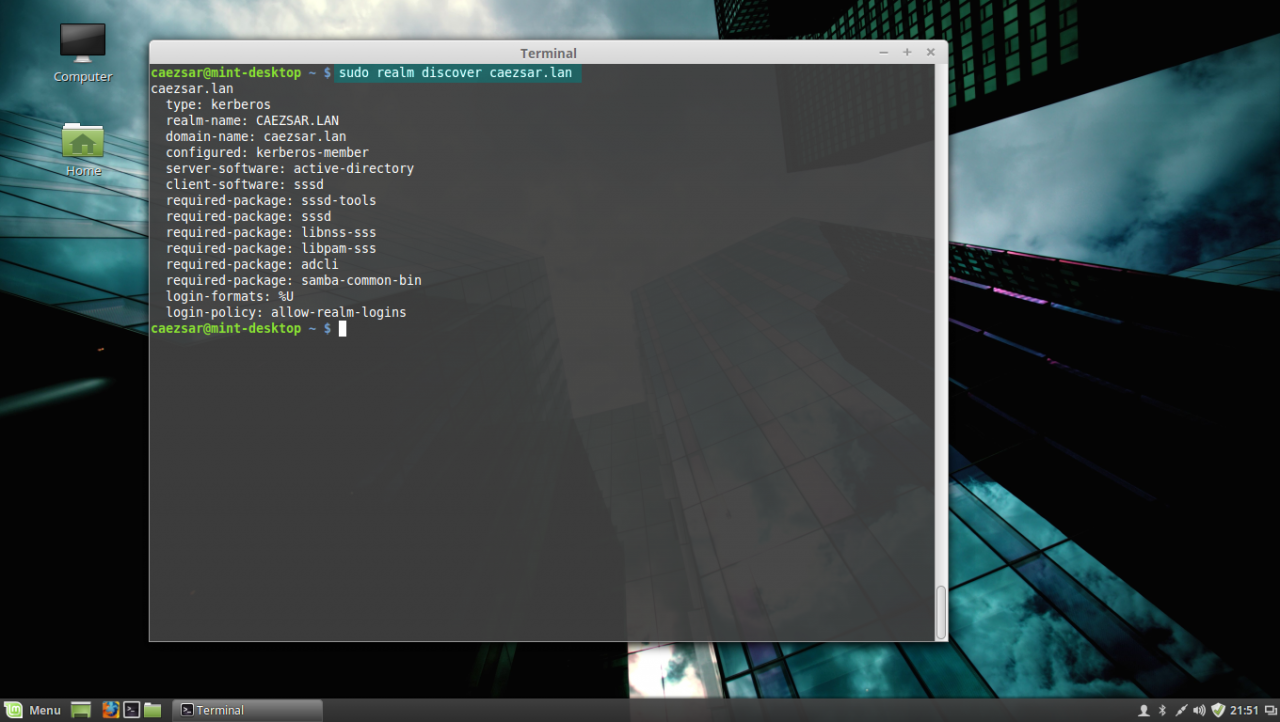
realm discover domain
10. If everything is correctly setup at the client side and the domain controller responds, issue the following command in order to integrate Linux Mint client machine to Windows Server 2012 AD PDC.
sudo realm join domain.tld -U domain_administrator --verbose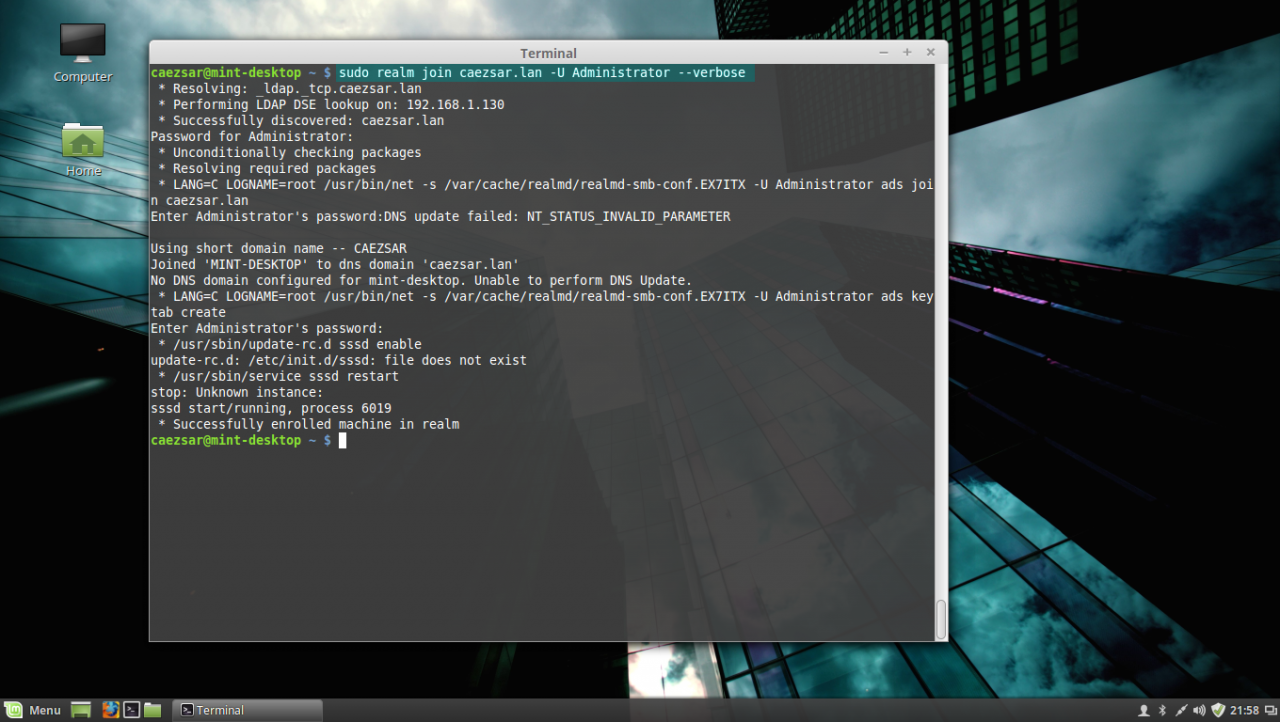
join AD domain
Use the -U option to specify an Active Directory administrative user with privileges to add machines on the server and the --verbose option to get debug output in case something goes wrong with the integration process.
Once the command returns successfully status and ads Linux Mint to AD you can use the sudo realm list command to view full details and the default configurations for your domain.
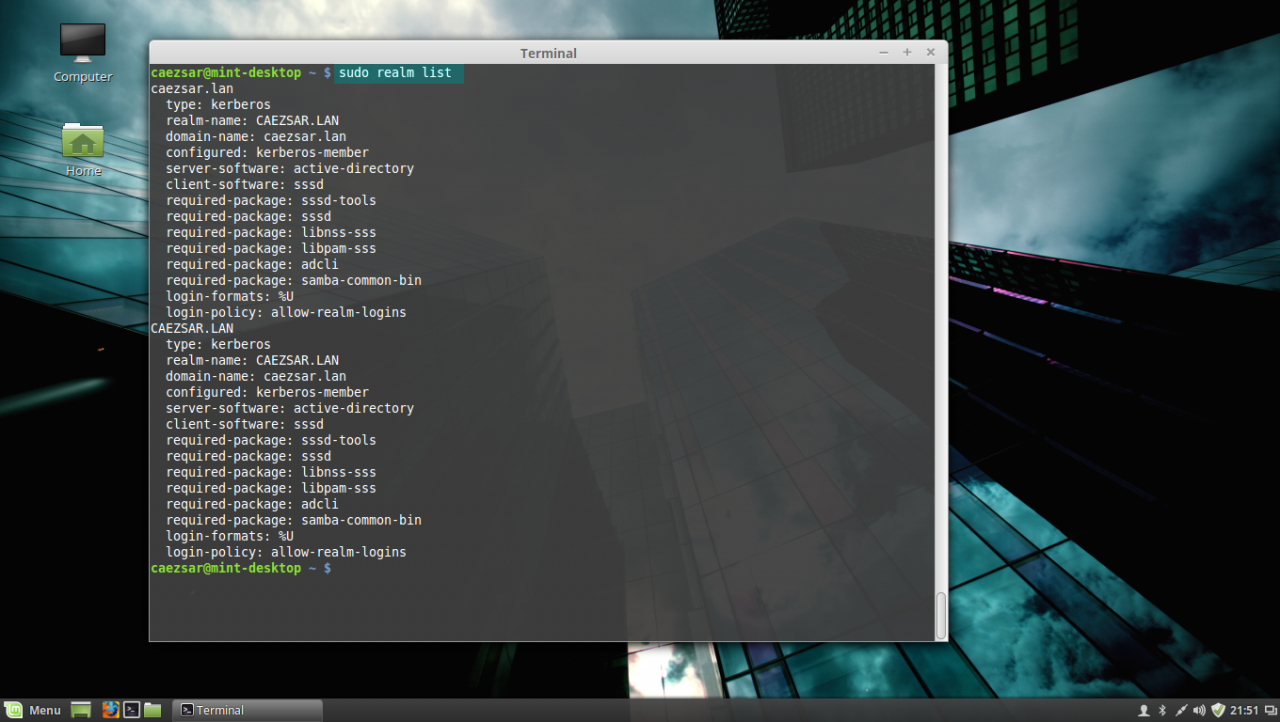
list realm
To manage sssd service use the following command switches (you don’t need to manually start the sssd service because it’s automatically started by the realmd when the machine is enrolled to realm):
sudo service sssd status|start|stop11. To check if the machine appears on the Domain Controller, go to your Windows Server 2012, open Active Directory Users and Computers utility and search your Linux Mint hostname.
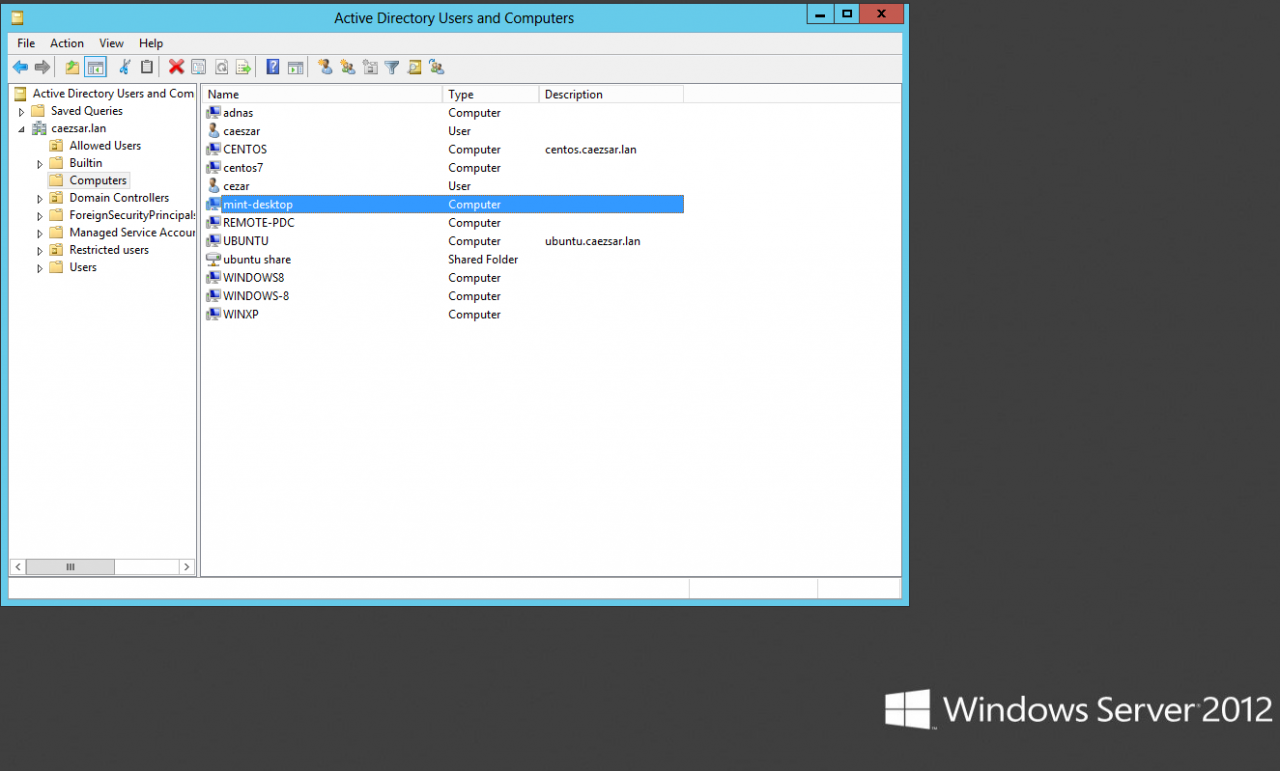
Active Directory Users and Computers
STEP FIVE – Log In on Linux Mint with Active Directory Accounts
12. To authenticate on Linux Mint with and an Active Directory user, first you need to add a permit rule on local policies in order to grant access for all realm users on local machine, by issuing the following command:
sudo realm permit --allTo grant access just for a specific AD user or group use the following command syntax:
sudo realm permit -u AD_usernamesudo realm permit -g AD_groupTo withdraw access for a user use the command with --x switch:
sudo realm permit domain --x domain\AD_username13. To perform Terminal console command line authentications on Linux Mint host with an Active Directory account, use double backslashes to escape the backslash which separates the domain string from user, as shown in the below syntax (you can append the dot domain or use just the domain string):
su - domain.tld\\AD_usernameor
su - domain\\AD_username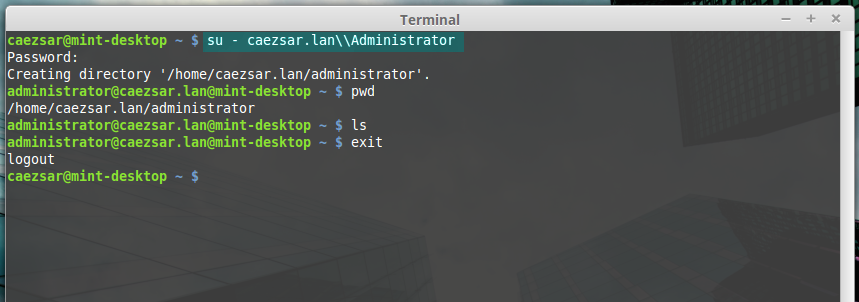
AD user login
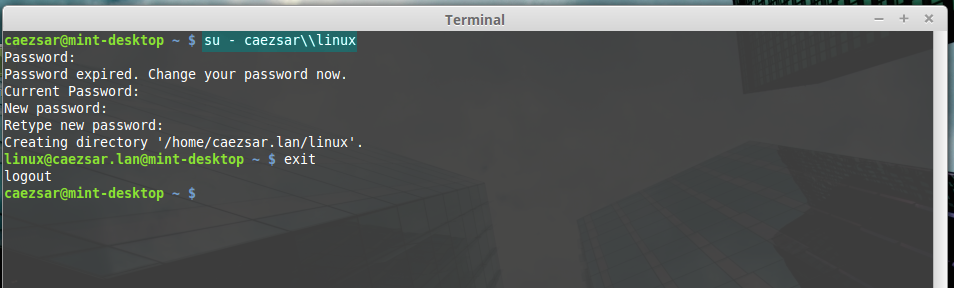
ad user login without dot domain
14. To log in with an AD account on Linux using Putty or to perform Linux Mint MDM GUI logins use the following syntax:
domain\AD_username
domain.tld\AD_username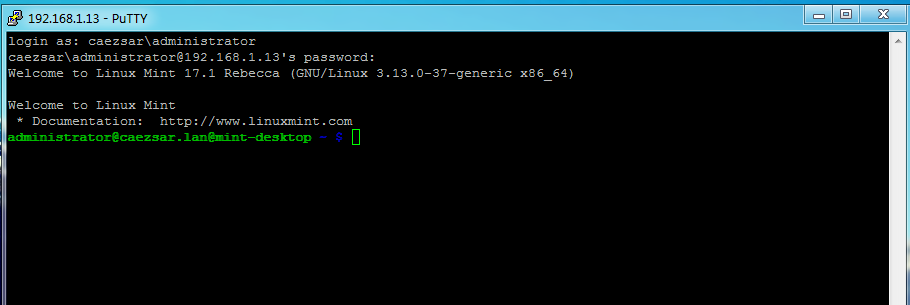
AD user Putty login
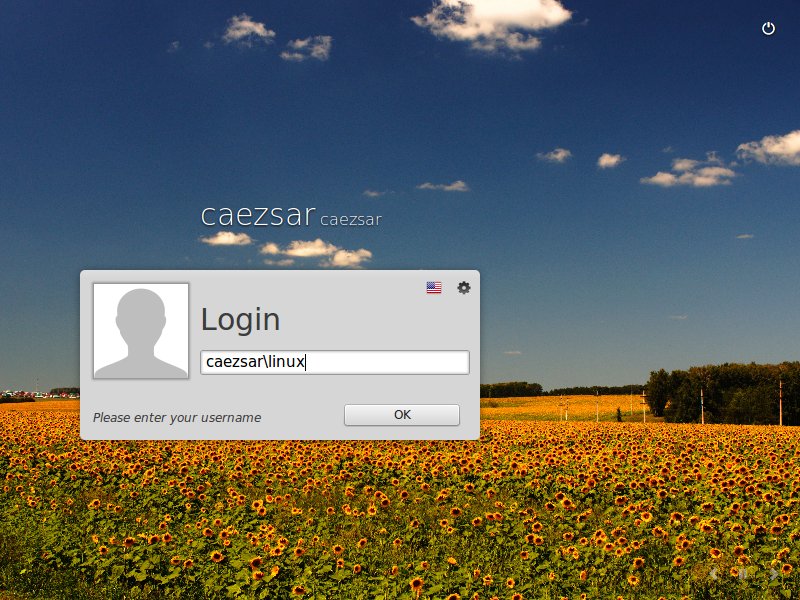
Ad user GUI login
15. In case you have issues with AD users authentication on Linux Mint Logon Screen, log in with a local user account and change the Login Window Theme from an HTML theme to a GDM theme, log out, hit Escape key is case the last logged in user appears on username Login filed and continue the authentication process with a AD account as presented above.
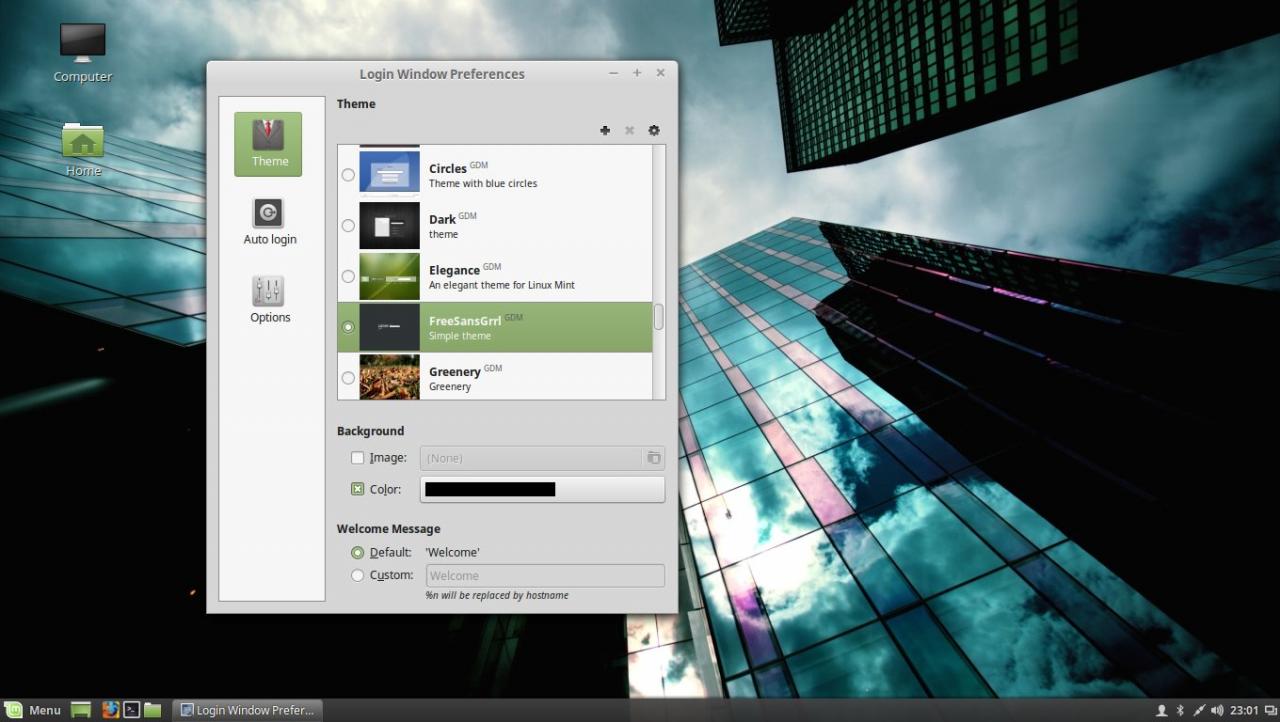
Use GDM theme

GDM login screen
STEP SIX – Add Root Permissions to AD Domain Admins Users
16. In case you want to allow all Active Directory Domain Admins to have full administrative permissions in order to execute any command with root privileges on the Linux Mint machine, open the local sudoers file for editing and add the following line:
sudo nano /etc/sudoersor
sudo visudoAdd this line after %sudo line:
%domain\ [email protected] ALL=(ALL) ALL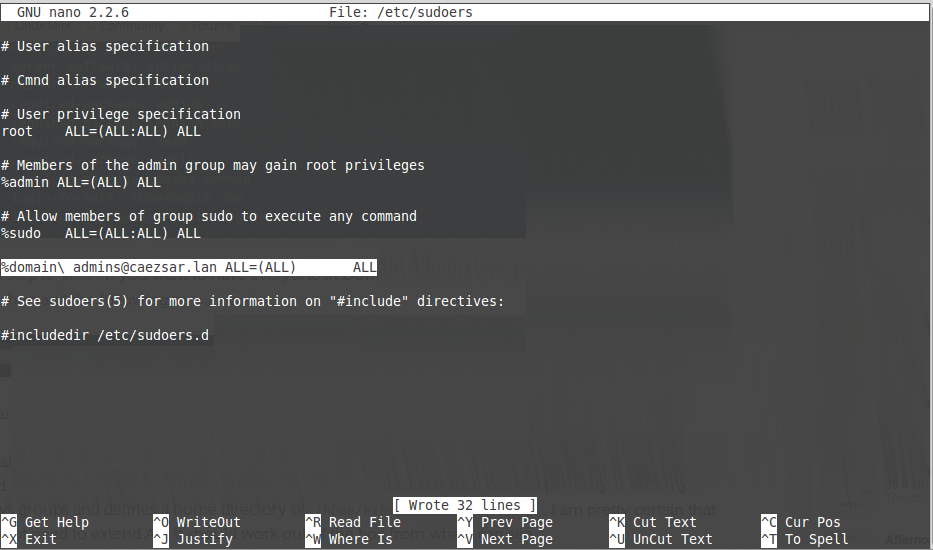
add domain admins root privileges
17. In case you don’t want your Linux Mint machine to be a part of the domain anymore, issue the following command to leave the domain:
sudo realm leave domain.tld -U AD_admin_user --verbose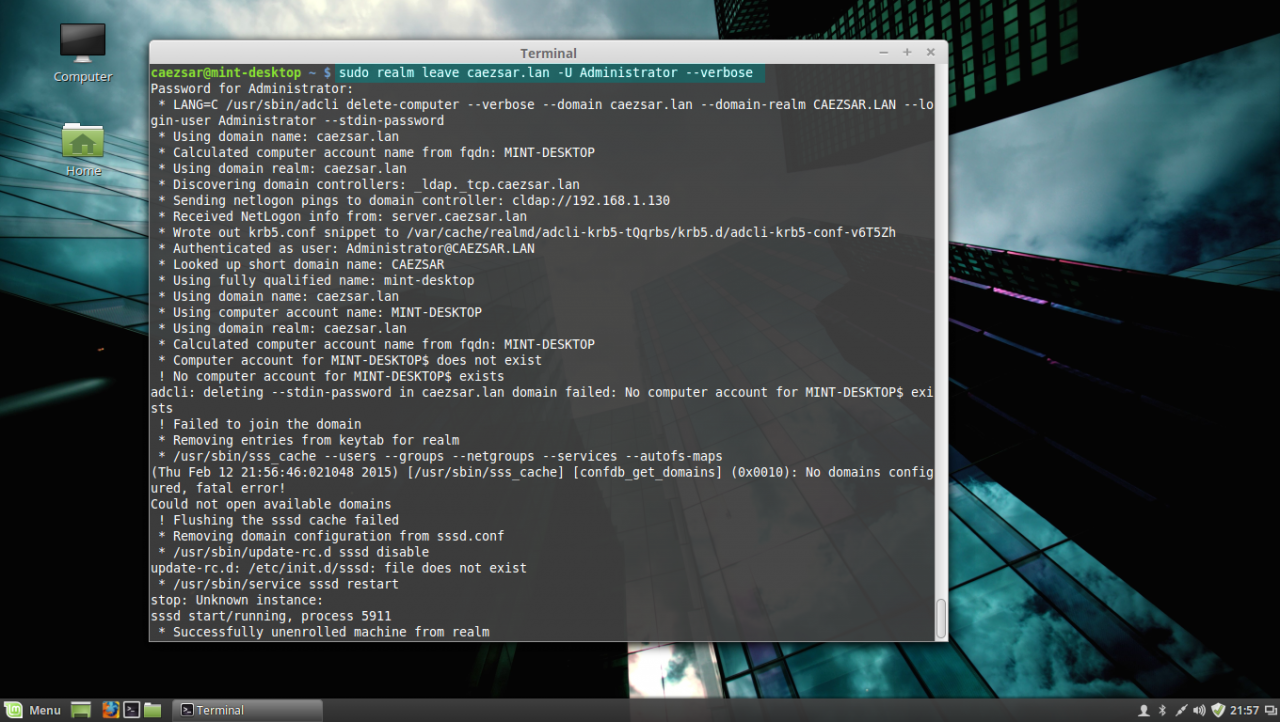
leave AD PDC
That’s all! Now, the machine running Linux Mint 17.1 is integrated as a part of Windows Active Directory Domain Controller and can successfully replace your old Windows XP machine, for which Microsoft has stopped its support, but keep in mind that some features and, especially, a huge part of Active Directory Group Policy, don’t apply on Linux systems.




Dear sir ,
without getting any error , all command run successfully on my linux mint client Os and network confirguration is also configured correctly, After this i checked on PDC server , hotname of linux mint not coming into computer category. Please help , Looking forward to hear from you soon.
i followed this tutorial,Ive got an error when trying to join to domain.it says
realm: Specify one realm to join. Any help would be appreciated.Thanks
not work for me in tep one , after apply network settings , when i do ping -c3 mydomain.lan
i have msg network no accecible .
but if i do ping ip_of_ADserver they work .
the resolt in step four (9) : sudo realm discover domain.tld
i have only 4 line :
my domain
type : kerberos
realm-name : mydomain
domain-name : mydomain
configured : no
i fellow the tutorial step by step wher is the problem
Everything works perfectly… up to the point of actually logging in as Domain user at which point your screwed… does not work.
Didn’t use everything in here since I mixed some tutorials, but most of this information was very helpful to get 19.3 up and running with my AD. Mint PC is in AD, homedir created automagically, etc. No try to get the homedir on my NAS.
Thanks!
DAVIDAPRIL 19, 2020 Reply
Everything works perfectly… up to the point of actually logging in as Domain user at which point your screwed… does not work.
Same here because the section about changing the login screen is dead wrong. You can’t change it. I can ssh into the machine as any domain user without a problem but I’ll be damned if the GUI login screen can be changed to allow DOMAIN user login.
It is not necessary to set up the DNS server manually.
1. There is no PDC in a Windows 2019 domain, there is only a PDC emulator on one of the domain controllers.
2. Each domain controller is always a DNS server.
3. A PC can only log on to a DC with a Global Catalog (GC).
4. An administrator who does not set up their DHCP server to transmit invalid information should change jobs.